Just to make sure you understand how AdGuard ad blocking works: AdGuard, a private company, provides a DNS server that is modified to that it pretends that ad servers don‘t exist. For example if your computer asks the server for the ip address for the fictitios „ads.google.com“ the answer will be NXDOMAIN which means there is no server with that hostname.
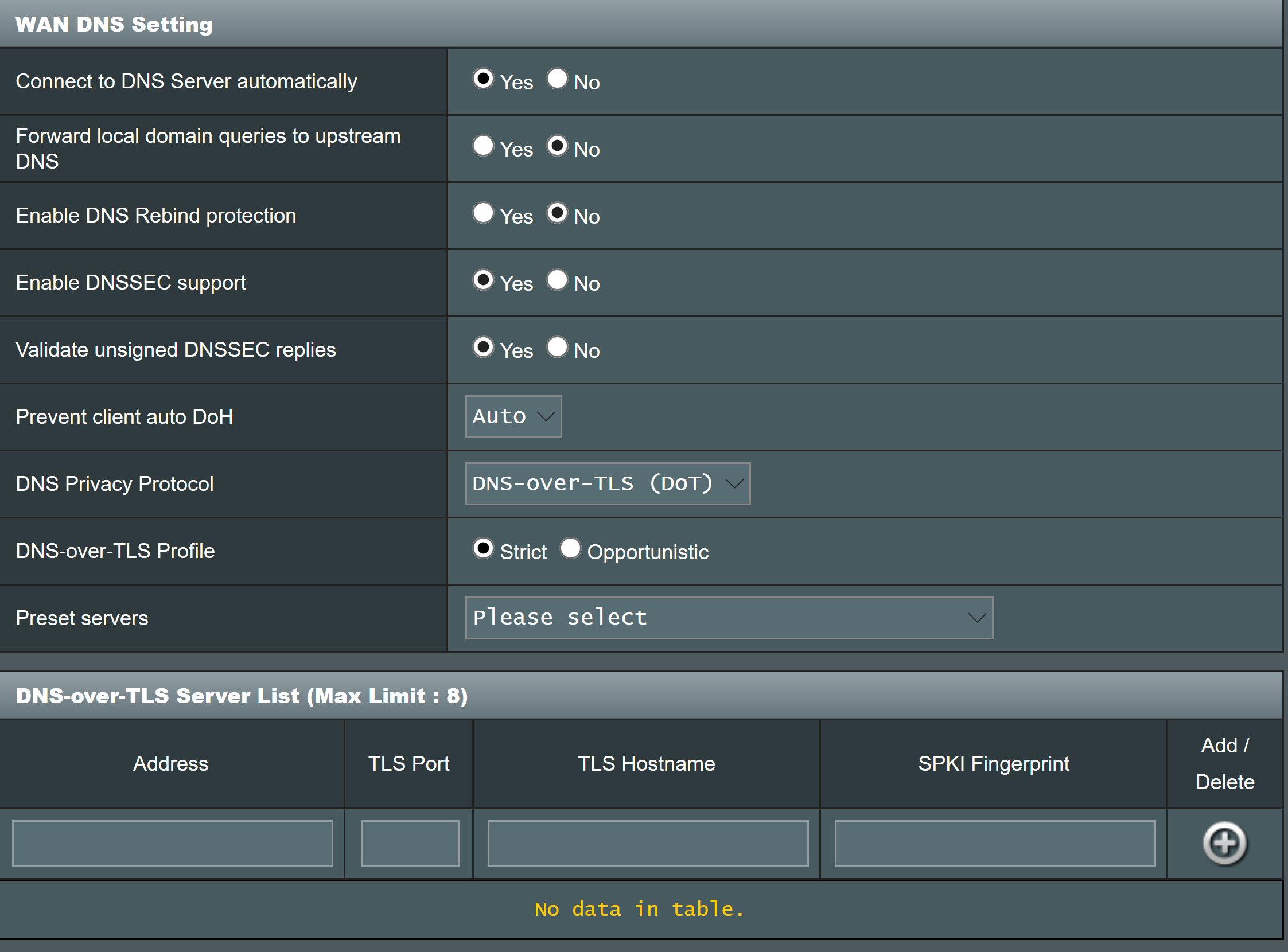
AdGuard actually provides a lot of different servers: normal DNS, DNS-over-TLS and DNS-over-HTTPS. AdGuard provides the ip address for normal DNS as well as the hostnames required for DNS-over-TLS and DoH on their setup page (
https://adguard.com/en/adguard-dns/overview.html#instruction under DNS privacy and DNS tabs).
There are variants with and without „family filter“. The family filter probably blocks pages the company doesn‘t deem child safe, which given that it is an US.-American company will probably mean a lot of sex stuff and way too little brutal stuff.
If you don‘t live in North America or other evil places that allow or force internet providers to inject ads, sell your DNS history, or try to censor specific pages then you can get away with just using normal DNS (without DNS privacy). If you need tamper proof and private DNS queries then you need to use DoTLS or DoH. DoH is much easier to setup, you only need to switch the method in the screenshot you provided and put in the hostname given on the AdGuard site.
Using google DNS as DoH or DoTLS host will give you tamper proof and private (from your ISP, not google) DNS, but not ad blocking. Be aware that Firefox is starting to roll out their own version of DoH in North America that ignores the DNS setting from your router and uses cloudflares DoH, which would mean that ad blocking wouldn‘t work in Firefox. There is a lot of discussion going on there still though, so you might want to stay posted.